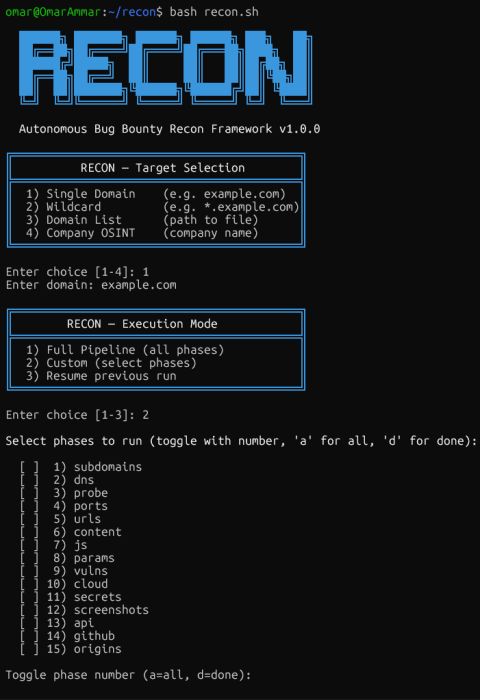
I just built “RECON” — an autonomous bug bounty recon framework.
One command. 30+ tools. 15 phases. Prioritized attack plan.
━━━━━━━━━━━━━━━━━━━━━━━
⚙️ WHAT IT COVERS
━━━━━━━━━━━━━━━━━━━━━━━
→ Subdomain discovery (11 sources, passive + active)
→ DNS mapping, live host probing, port scanning
→ URL harvesting, JS secrets, parameter discovery
→ CVEs, XSS, SQLi, subdomain takeovers
→ Cloud misconfigs (S3 / GCP / Azure)
→ GitHub dorking, credential leaks, origin IP bypass
━━━━━━━━━━━━━━━━━━━━━━━
🧠 INTELLIGENCE ENGINE
━━━━━━━━━━━━━━━━━━━━━━━
Not just a tool chain — “RECON” thinks after it scans:
• Detects anomalies (debug pages, SQL errors, exposed JWTs)
• Generates vuln hypotheses per endpoint
• Correlates multi-step bug chains (SSRF → metadata → RCE)
• Scores & ranks every target by exploitability
• Outputs a ready-to-execute action list
━━━━━━━━━━━━━━━━━━━━━━━
📦 OUTPUT
━━━━━━━━━━━━━━━━━━━━━━━
7 formats: HTML dashboard · Markdown report · findings.json · prioritized targets · HackerOne template · Burp Suite XML · machine-readable JSON
━━━━━━━━━━━━━━━━━━━━━━━
✅ KEY FEATURES
━━━━━━━━━━━━━━━━━━━━━━━
⚡ Smart resume — crash mid-scan, pick up where you left off
🔄 Differential recon — surface only new assets across runs
🌐 Distributed scanning — split load across VPS nodes
🔔 Live alerts — Telegram, Discord & Slack per phase
🔌 Burp integration — proxy routing + Pro REST API support
━━━━━━━━━━━━━━━━━━━━━━━
Who it’s for: Bug bounty hunters · Pentesters
Runs on Ubuntu / Kali · Under 15 min install
Built to automate the 70% so you can focus on the 30% that actually requires a human.
Responses (0)
Join the Conversation
Have an account? Logging in lets you customize your avatar and keeps your comments connected to your profile.
Log In or Register